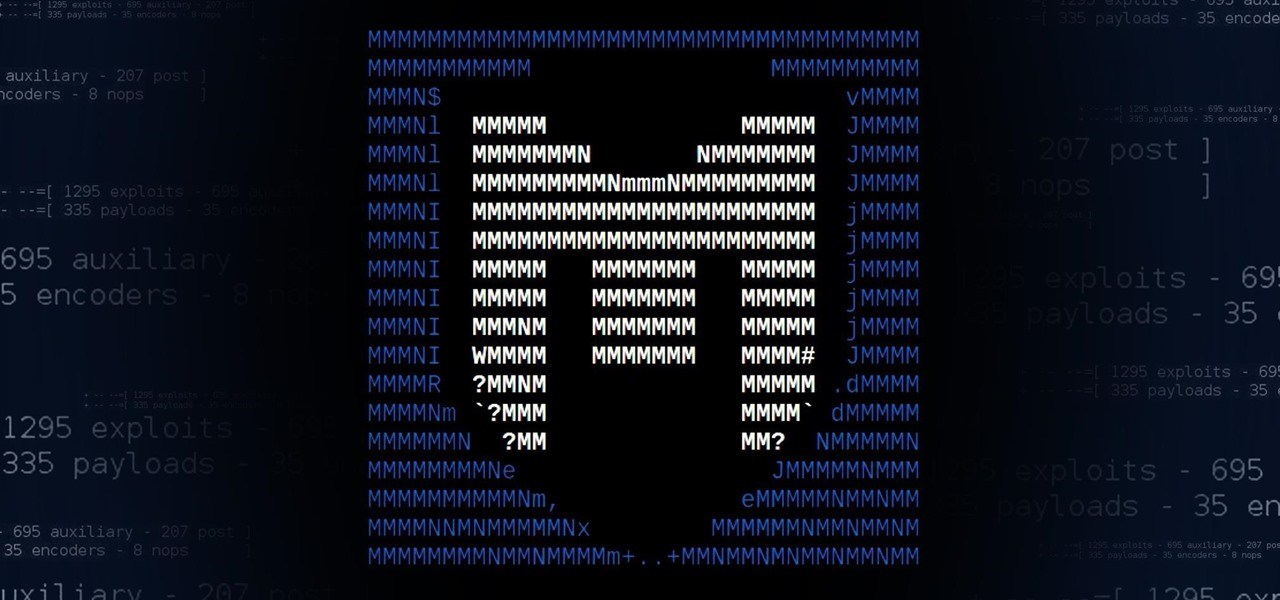
What is Metasploit?
Metasploit is a pen testing framework which is used by both ethical hackers and malicious attackers to analyze vulnerabilities within a system, network or server. It is also an open source framework, making it highly modifiable by anybody who has the knowledge of penetration testing. It is highly flexible between various operating systems.
Metasploit lets you work with custom codes that are premade for convenience. These codes are usable to probe the weaknesses within the network. You can use these identified weaknesses as documented information to analyze which solutions should be deployed. Metasploit is a great convenient method to discover the various conflicts that lie within the servers.
You can get the program directly from the Rapid7 website.
How It Came To Be
Developers H.D. Moore and Matt Miller wanted to provide a Perl-based network tool in 2003. They executed the Metasploit Project in that year but was converted to Ruby in 2007. In 2009, Rapid7 acquired the license to the project. It became a tool that was viable for targeting remote exploitations and anti-forensic solutions.
Since then, it became the mitigation tool for cyber security professionals as it became easier for them to use Metasploit rather than probing with various tools that they do not know if they were effective for a weak spot. The convenience of remote testing spread throughout the entire world. What used to be a special tool only used in local areas and private companies is now a free tool for anybody to use.
Who Uses Metasploit
Anybody is free to use the framework but it is primarily used by DevSec operators and hackers. It is a tool used for both good and evil, depending on whoever is using it.
Thanks to its constant updates, Metasploit provides more than 1677 exploits. These exploits are found in 25 platforms like Python, Java, Cisco, and Android. As for payloads, it includes over 500 of them such as command shell payloads for running scripts against the host’s will, dynamic payloads which lets you generate unique payloads to trespass antivirus protocs, a meterpreter payload which lets you take control over the monitors with VMC so you can possess the machine and do whatever you want with it like uploading and download files, and static payloads which allow port forwarding and various network communications.
The Importance of Metasploit
Metasploit is now a crucial framework for anybody within the security analysis and penetration testing field. It gives them a glimpse of how malicious attackers can slither through even the toughest systems in the world and provides them the knowledge on how to deploy countermeasures.
This free tool has become one of the main sources for cybersecurity, making it the backbone of both ethical hackers and malicious hackers. It keeps on evolving everyday with more exploits and solutions for the benefit of better security protocols in the future.